You might think cybersecurity is only for Fortune 500 companies. Wrong. In New Jersey, small businesses face the same threats and are increasingly targeted. With the New Jersey Data Privacy Act (NJDPA) enforcement deadline on July 1, 2026 (just months away), the stakes are critical. Sixty percent of businesses that suffer a data breach close within six months. That’s not just because of the attack; it’s the loss of customer trust and the legal costs that follow.
Why Small Businesses Are Perfect Targets
A seven-person CPA firm in New Jersey got hit by ransomware. The $15,000 ransom destroyed them, not just the downtime, but three clients left. Eight months later, the firm shut down. White Realtors paid $1.2 million for a data breach. RCCA paid $425,000. These aren’t tech companies. They’re local businesses like yours.
Why are they targeted? Three reasons:
- Lower defenses – you don’t have a 24/7 security team. Attackers know this.
- Valuable data – you have credit cards, SSNs, and health records. Your data is as valuable as any Fortune 500 company’s.
- Supply chain access – if you work with larger clients, you’re the back door that attackers use to breach them.
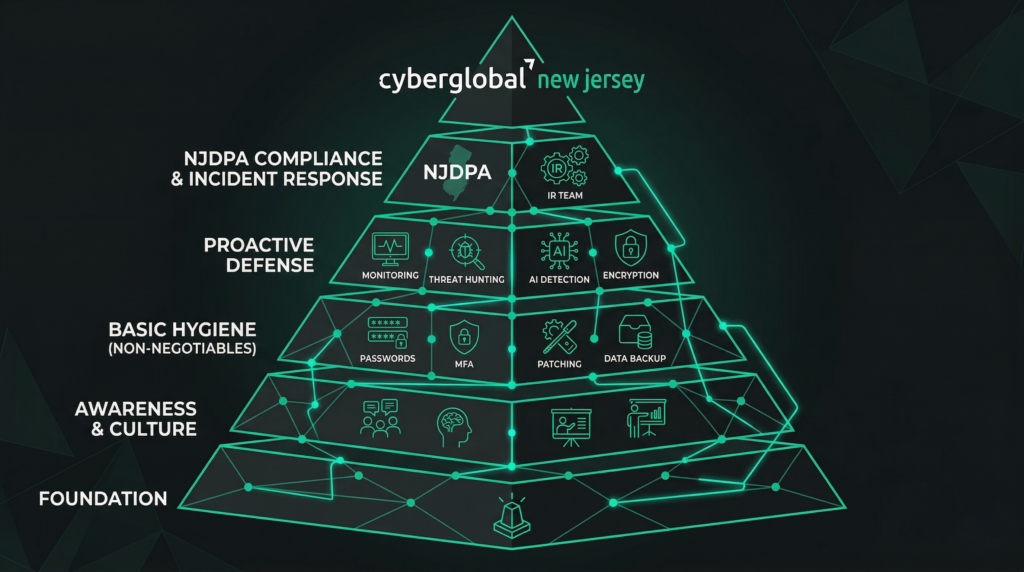
The Five-Layer Defense Pyramid
Cybersecurity isn’t about expensive tools. It’s about defending people, technology, and processes. Here are the five layers you need:
Layer 1: Awareness & Culture
Sixty percent of breaches involve human error. Your employees are your strongest defense. Implement
monthly 10-minute security moments, annual phishing training, and creating a safe culture where people
report suspicious emails without fear.
Layer 2: Basic Hygiene (Non-Negotiables)
- Multi-Factor Authentication (MFA): This protects 99% of automated phishing attacks. If you have no MFA, when breached, your cyber insurance won’t pay.
- Strong Passwords: Use a password manager (LastPass, 1Password, Bitwarden) so you don’t reuse passwords.
- Regular Patching: Update immediately when patches are released.
- Offline Backups: Follow the 3-2-1 strategy (3 backups in 2 locations with 1 offline) to protect against ransomware.
- Vendor Contracts: Ensure all third parties have NJDPA-compliant data processing agreements.
Layer 3: Proactive Defense
Don’t wait for attackers to find your vulnerabilities. Conduct penetration testing to identify weaknesses before they do. Use vulnerability scanning to monitor your network for anomalies. Monitor the dark web to see if your data has been leaked.
Layer 4: NJDPA Compliance
Who must comply? Any organization processing data of 100,000+ NJ consumers annually, or 25,000+ if you derive revenue from that data. Enforcement: July 1, 2026 (no grace period after). Penalties: $10,000 first violation, $20,000 each subsequent. What’s required: Honor consumer rights (access, deletion, opt-out), obtain opt-in consent for sensitive data (health, biometric, financial, geolocation), conduct Data Protection Assessments for high-risk processing, and maintain audit-ready documentation.
Layer 5: Incident Response
The average breach goes undetected for 27 days, meaning attackers are in your system for 7 months before you know. You need a documented incident response plan with clear escalation procedures, contact information for your IT provider and insurance company, and a tabletop exercise to test your response. Consider an incident response retainer so someone picks up the phone within 2 hours if disaster strikes.
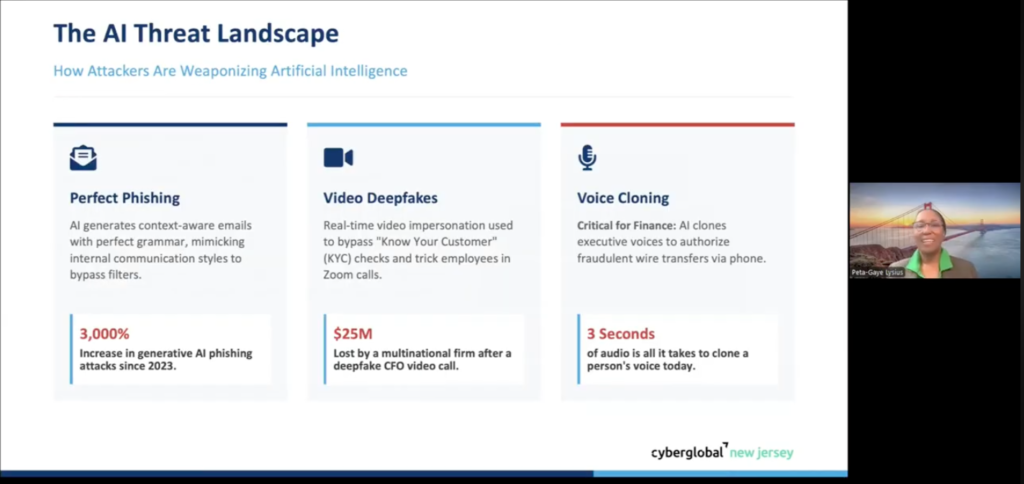
The AI Threat Landscape
AI has changed attack tactics dramatically. AI Phishing (3,000%+ increase since 2023): AI generates
context-aware emails with perfect grammar that mimic your boss’s writing style. These emails reference
internal projects and personal details because attackers scrape this info from LinkedIn and company
websites.
Video Deepfakes: A multinational firm lost $25 million when an employee authorized a wire transfer after a deepfake video call from someone appearing to be their CFO.
Voice Cloning (3 seconds of audio): A UAE bank lost $35 million when attackers cloned an executive’s voice to request wire transfers. This is now targeting US credit unions.
Defense: Train employees to verify unusual requests through alternate channels. Implement dual authorization for financial transactions. Never rely on video or voice alone for sensitive approvals.
Your 90-Day Action Plan
Days 1-30 (CRAWL):
- Enable MFA on everything – email, VPN, cloud services, admin accounts.
- Deploy a password manager so your team uses strong, unique passwords.
Days 30-60 (WALK):
- Audit your MFA – is it actually enforced everywhere?
- Run a vulnerability scan of your infrastructure.
- Review third-party contracts for NJDPA compliance.
- Start building your incident response plan.
Days 60-90 (RUN):
- Implement automated monitoring and alerting.
- Conduct a penetration test.
- Finalize and test your incident response plan with a tabletop exercise.
- Ensure full NJDPA compliance.


Key Takeaways
- Size doesn’t protect you; it makes you a target. The difference between survival and shutdown is having a plan.
- Cybersecurity is ongoing, not one-time. Software updates can disable MFA. Employees leave without account deactivation. Security requires constant attention.
- ROI is undeniable. A $10K investment in cybersecurity prevents a $4.4 million average breach cost.
- NJDPA enforcement is coming in 3 months. The grace period ends July 1, 2026. Document everything now and get audit-ready.
- You don’t have to do it alone. Work with your IT provider, insurance company, and a qualified cybersecurity firm. The cost of expert guidance is far less than the cost of a breach.
Watch the Full Presentation
For deeper learning, watch the complete NJBIA Leadership Training Series presentation featuring me, Peta-Gaye Lysius, and Dan Gizzi. Topics include the five-layer defense pyramid in detail, a real breach case
studies, AI threats, live Q&A, and tactics you can implement immediately.
Get Started Today
CyberGlobal New Jersey is your local cybersecurity team. We specialize in helping small and mid-sized businesses achieve NJDPA compliance and reduce cyber risk. We offer NJDPA assessments, penetration
testing, security awareness training, incident response planning, and full compliance management.
Phone: 732-208-4272
Email: petagaye.lysius@cybergl.com
Don’t let your organization become an enforcement example. The time to act is now.



